Detecting and responding to a Data Breach correctly could save your business. The frequency and complexity of cyber threats continue to grow at an unprecedented rate. The era of believing that a data breach ‘couldn’t happen to us’ is long past. Today, businesses must confront the reality that a data breach is not just probable, but almost inevitable. With this in mind, it becomes crucial to understand how to detect and respond swiftly and effectively to these threats.
In this comprehensive blog, we explore the cybercriminal’s mindset, the techniques they employ, and the devastating effects of a data breach. More importantly, we provide strategic insights into how to identify and respond to these breaches, underlining the significance of Managed Detection and Response (MDR) solutions.
We also delve into the essential steps to take in response to a data breach and the importance of continually updating your Disaster Recovery Plan. Our aim is to equip organisations with the knowledge to not only defend against cyber-attacks but to react efficiently and effectively when they occur, thereby protecting their valuable data and preserving their hard-earned reputation.
The Attacker’s Perspective
From the standpoint of a cyber attacker, their primary interest lies not in legalities, but in obtaining profits through the illicit sale of compromised data. These nefarious individuals aim to infiltrate systems surreptitiously, embed themselves without detection, and establish clandestine access points.
Their ultimate objective is to manipulate compromised systems to capture, sometimes alter, and subsequently sell any valuable information for financial gain. Recognising the signs of a data breach is crucial to safeguarding your organisation.
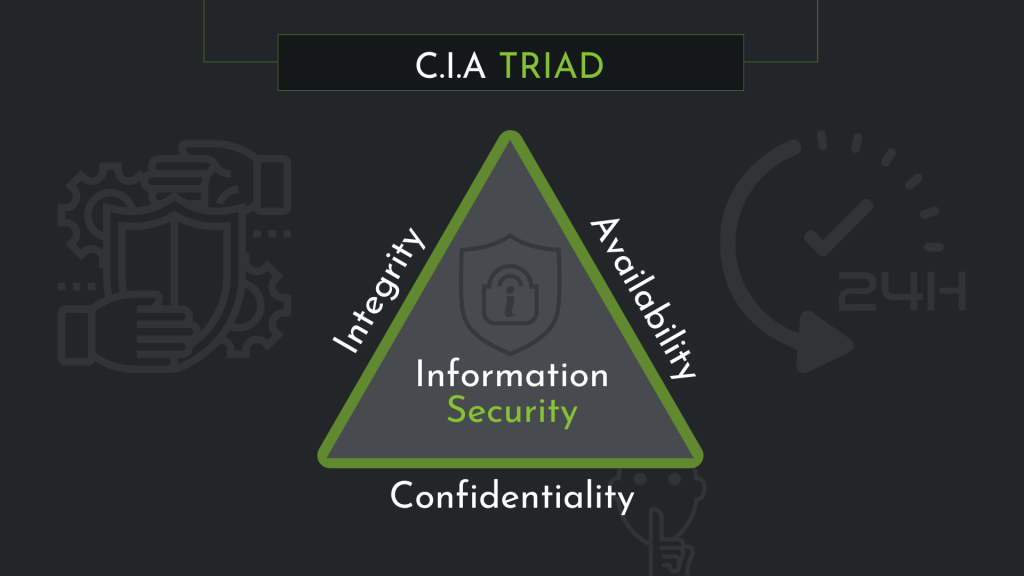
What is the CIA triad?
Data breaches are unfortunately a common occurrence and often seen as inevitable. The advent of new technologies has heralded a new era of increasingly sophisticated cyber threats. All cyber security strategies should give prominence to data integrity, confidentiality, and availability, as we have previously discussed in our Threat, Vulnerability, & Risk blog. An essential goal is to minimise dwell time — the period an attacker remains undetected within a company’s network. Swift detection and effective resolution of breaches offer the greatest value, a benefit provided by a well-orchestrated Managed Detection and Response (MDR) solution.
Globally, the average dwell time exceeds 100 days. In many instances, security teams are oblivious to a data breach until notified by a supplier, client, or business partner, typically following receipt of a fraudulent email instructing payment redirection to a new bank account.
Such breaches not only endanger business relationships but can also impose substantial financial liabilities. Data breaches typically manifest in two forms: impersonation, where a criminal masquerades as a company using a similar domain name and email address; or compromise, where the fraudulent email originates from the company’s own system. The latter situation raises questions regarding financial responsibility for losses incurred by a business partner.
This approach to cyberattacks, such as phishing, completely circumvents traditional cybersecurity measures like antivirus software and firewalls, which many businesses continue to rely on. While 80% of companies attribute breaches to phishing attempts, 28% cite impersonation of an organisation in emails or online as the causative factor. Only 27% blamed viruses, spyware, or malware, including ransomware attacks, for the breach.
Mitigation
Many businesses continue to place reliance on perimeter security. Those that do should pose some pertinent questions to themselves. Firstly, can you confidently state that your business remains unharmed? How would you know if the attacker didn’t utilise malware or a virus that your perimeter defences would detect? Secondly, many companies are uncertain about the necessary steps following a detected data breach.
Can you confidently determine where your company has been compromised if a supplier informs you of a breach? What part of your business has been affected? What is the primary objective of the attack?

The General Data Protection Regulation (GDPR) recognises that the risk associated with a cyberattack extends beyond financial loss, as attackers actively seek to access personal information. Therefore, data confidentiality, integrity, and availability should all be integral to security measures. However, given the current threat landscape, organisations must accept that complete protection is unattainable, requiring a fundamental shift in security thinking.
Preventing attacks is impossible when hackers employ the same tactics and tools as legitimate users. Early detection and remediation should be prioritised.
Identifying a Data Breach
Unexpected System Activity: Keep an eye out for unusual system activity. This might include repeated failed login attempts, unfamiliar user accounts, or unexpected software installations.
Abnormal Network Traffic: Unusual patterns of network traffic, particularly during off-peak hours, might signal a breach.
Irregularities in User Behaviour: Uncharacteristic behaviours from legitimate users, such as changes in the amount or type of data accessed, could indicate compromised accounts.
Security System Alerts: Regularly review reports and logs generated by your security software. These tools often provide the first indication of a breach.
Data Discrepancies: Unexplained changes in files or databases, such as alterations, deletions, or unexpected transfers, are often signs of a breach.
Responding to a Data Breach
Confirm the Breach: Once a potential breach is detected, it’s crucial to verify its existence and scope. Engage your IT team or a trusted cybersecurity firm to investigate.
Containment: After confirming the breach, take immediate steps to limit its impact. This might involve disconnecting affected systems from the network or changing access credentials.
Assessment: Determine the extent of the breach. What data was affected? Was it encrypted? Is the vulnerability that allowed the breach still present?
Notification: In the UK, the General Data Protection Regulation (GDPR) mandates that data breaches be reported to the Information Commissioner’s Office (ICO) within 72 hours. Affected individuals should also be informed if there’s a high risk to their rights and freedoms immediately.
Remediation: After containment and assessment, address the vulnerabilities that led to the breach. This may involve patching software, updating security protocols, or enhancing user training.
Learning from the Incident: Conduct a post-incident review. What went right in your response? What could be improved? Use these learnings to strengthen your security posture.
Managed Detection & Response (MDR)
MDR allows a business to identify unusual activities indicative of a security compromise. Such activities warrant investigation if a user accesses files they wouldn’t typically view, sends unexpected emails, or visits a new website. However, most businesses lack the resources to detect this behaviour and the time and expertise to discern whether it constitutes a breach or a false positive.
An MDR approach not only alleviates strain on the business but also allows each organisation to benefit from a collective pool of knowledge gained from identifying and resolving threats. Every incident detected by MDR is investigated and, if a data breach is confirmed, managed.
This involves severing the communication channel of the attack, preventing the attacker from maintaining contact with the compromised system, and identifying any affected assets. These can be remedied either internally or as part of the MDR service.
Moreover, data regarding the method of attack is collected. This prompt, actionable intelligence is immediately incorporated into the MDR service, resulting in either a preventive or detection mechanism to minimise the probability of a repeat attack.
Consequently, the speed at which attacks can now be detected is convincing – while the average dwell time has been decreasing in recent years, unknown malware can now be detected and eliminated in less than an hour.
Understanding the Threat Landscape

The threat landscape is perpetually evolving, necessitating businesses to acknowledge this and adapt their security tactics to the actual level of risk. Additionally, while increased board-level commitment to security is commendable, businesses must not equate expenditure with efficacy.
Organisations must address the implications of data loss, but also the consequences for data integrity and availability. In the event of a breach, an organisation must understand what transpired, and security policies can no longer depend on users not making errors.
Security strategies must not remain static. Given the rise of phishing and diversion fraud, simply securing the perimeter is no longer sufficient. While businesses can’t prevent all attacks, it’s crucial to comprehend how, when, and why an attack is successful, enabling the selection of an appropriate response and lessons to be learned for the future. Only with this approach can organisations effectively safeguard their business, data, and reputation.
In conclusion, while it’s impossible to provide absolute protection from all internet threats, smart businesses dedicate the necessary time and resources to breach recovery plans. According to recent statistics, human or process errors are responsible for four out of every five data breaches. The critical point is that these are entirely avoidable with proper planning and preparedness.