Introduction
In the expansive landscape of cyber security careers, opportunities abound across a diverse range of specialisations. Whether you’re inclined toward roles like Security Operations Centre (SOC) analysts or prefer steering the ship from management positions, there’s a niche for every skill set. Among these, penetration testing stands out as a particularly noteworthy career path. If you’re contemplating a penetration testing career, this article is tailored specifically for you.
What is Penetration Testing?
Penetration Testing, often referred to as “ethical hacking,” is a comprehensive practice aimed at evaluating the security of digital assets by simulating cyber attacks against them. The objective is to identify vulnerabilities, weaknesses, and potential entry points that malicious hackers could exploit. This critical cyber security function can be applied across various domains, including but not limited to mobile applications, web applications, cloud environments, infrastructure, and Application Programming Interfaces (APIs).
Given the vastness and complexity of the field, penetration testers often choose to specialise in one or more specific areas. Specialisation allows them to delve deeply into the nuances and intricacies of a particular domain, thereby becoming experts capable of identifying even the most subtle vulnerabilities. This level of expertise is crucial, as the cyber security landscape is ever-evolving, with new types of threats emerging regularly. By focusing on a niche, penetration testers can stay ahead of the curve, continually updating their skills and methodologies to counteract the latest security threats effectively.
What skills are necessary to become a penetration tester?
When considering a penetration testing career, the skill set required is frequently underestimated. At its core, penetration testing is a multidisciplinary field that demands a broad range of technical and soft skills. While a degree in computer science or a related field can provide a strong foundation, it’s not an absolute prerequisite. What’s more crucial is a deep understanding of computer systems, networks, and security protocols, as this foundational knowledge serves as the bedrock upon which you can build specialised skills.
One of the key attributes of a successful penetration tester is a disciplined approach to continuous learning. The cybersecurity landscape is ever-changing, with new vulnerabilities and attack vectors emerging regularly. Therefore, a commitment to staying updated on the latest trends, tools, and techniques is essential for career advancement.
In addition to technical acumen, soft skills like problem-solving, analytical thinking, and effective communication are invaluable. Penetration testers often need to translate complex technical findings into actionable insights that can be easily understood by non-technical stakeholders. This ability to communicate effectively is crucial for both identifying vulnerabilities and advocating for the necessary changes to improve security.
Let’s get more specific on things you should consider when trying to break into the industry.
What hard skills are required for a penetration testing career?
- Thorough understanding of Computer Networks. (Network Protocols, OSI Model, Wireless Networks)
- Understanding of network hardware, what they do, and common misconfigurations with them. (Routers, Firewalls, Switches)
- How the internet works, and the underlying technologies that makes the internet function. (DNS, Routing, Web Servers)
- Common vulnerabilities. (Think OWASP Top 10)
- The common operating systems and how to use their command line interfaces. (Windows, Linux, MAC)
- Penetration testing requires a thorough understanding of how computers, servers, and network appliances operate. If you have experience in hardening and configuring a server, you will have a much better understanding of where to look for misconfigurations.
- Understanding of at least one programming or scripting language. (The most popular being Python and BASH)
- Understand your tools. During a penetration test, whether it’s infrastructure, web, mobile or API testing, understanding what tools to use and when, is critical to becoming a proficient penetration tester. You don’t need to understand how every tool works on a programming level, but you should understand the switches/flags and what they are doing.
- Ability to interpret the results of vulnerability scanners. Nessus, OpenVas, Burpsuite’s scanners all report false positives. Can you recreate the issue identified by the scanner and rule out a false positive?
What soft skills are required for a penetration testing career?
Soft skills are an important component when considering a career in penetration testing. Some people are natural orators, others have great difficulty communicating their thoughts and findings with clients. Not every penetration tester will be gifted with this ability, it is often something they will have to learn. Below is a list of skills and abilities that any penetration testing company will look for when looking to hire a penetration tester:
- A penetration tester must be able to act on their initiative and think independently.
- Thinking like an attacker. Okay, so you can follow a methodology, but can you think like an attacker does? If you can pop an alert box on a system. Can you demonstrate that you can steal insecure session cookies? A penetration tester needs to be able to demonstrate the impact of a specific vulnerability.
- CVSS scoring: The industry standard for categorising and scoring a vulnerability is CVSS scores. Not all clients will ask for this, but you should be able to demonstrate to a client what the impact of a vulnerability is.
- In today’s remote working environment, the ability to effectively communicate with clients is paramount, especially for roles like penetration testing. Whether you’re using video conferencing software for client calls to discuss scoping issues, debrief on findings, or provide an application overview, it’s essential to articulate your points clearly. Debrief calls are commonplace in this field; clients may not fully understand your report or may need further clarification on how a vulnerability was exploited. Therefore, it’s crucial to be able to discuss any issues or concerns you have about the testing scope, as well as to communicate high or critical-risk issues in a manner that is meaningful to the client.
- The ability to document technical findings in plain English (English is not a requirement). Generally, each vulnerability will have a title, risk rating (CVSS), description, evidence, remediation, and references that may help the client remediate the issue identified. You should be good at finding quality references for the report.
That’s a lot to learn. But if somebody is serious about a Penetration Testing Career. Having a good understanding of the above will go a long way. Soft skills are something that comes with experience. A Graduate or Junior Penetration Tester will not be likely to understand all of the above, and the soft skills will take some time to learn. A penetration testing company will be able to identify the potential of a person during the interview process.
What organisations are trusted in cyber security?
If you are learning how to report on issues found during a penetration test. You should have a good understanding of which organisations are trusted in cyber security. You will come across these organisations in your penetration testing career every week.
- ISC² (International Information System Security Certification Consortium) – Known for the CISSP certification, ISC² is a leading organisation for information security education and certifications.
- SANS Institute – Provides a variety of cyber security courses and certifications, including some focused specifically on penetration testing like the GWAPT.
- Offensive Security – Known for the OSCP (Offensive Security Certified Professional) certification, this organisation is focused specifically on penetration testing and offensive cyber security tactics.
- CREST (Council of Registered Ethical Security Testers) is a not-for-profit accreditation and certification body for the technical information security industry. Established in the United Kingdom, CREST serves to set high professional standards within the cybersecurity and penetration testing sectors. The organisation provides a framework of accredited professional qualifications and certifications for individuals and companies, ensuring that they meet rigorous and consistent standards.
- OWASP (Open Web Application Security Project) – Not a certification body, but an important organisation that provides free tools, methodologies, and guidelines on web application security, including penetration testing.
- EC-Council (International Council of E-Commerce Consultants) – Known for the CEH (Certified Ethical Hacker) certification, this organisation offers various training programmes in cyber security.
- ISACA – Offers the CISM and CISA certifications and is focused on governance, risk, and compliance in addition to cyber security.
- CompTIA – Provides the Security+ and CySA+ certifications, which are often considered entry-level certifications for cyber security professionals.
- NIST (National Institute of Standards and Technology) – A U.S. government agency that publishes an array of cyber security standards and best practices.
- CIS (Center for Internet Security) – Provides critical security controls and benchmarks that organisations can follow to improve their security posture.
- IACR (International Association for Cryptologic Research) – Focuses on the academic and research side of cyber security, particularly in cryptography.
- MITRE – Manages federally funded research and development centres supporting various U.S. government agencies. Known for the ATT&CK framework which is widely used in cyber security.
- Sencode Cyber Security – No list would be complete without shameless self-promotion.
What tools do Penetration Testers use?
This is like asking what ingredients a chef uses. It is all dependent on the recipe. The tools for attacking web applications are different from the tools for attacking infrastructure. Below you will find some tools that you should learn, along with our insights on each tool.
- NMAP “Network Mapper”: This tool is the bread and butter of a penetration tester, NMAP is several decades in the making. You can utilise NMAP to scan TCP/UDP ports, alongside the plethora of NMAP scripts that can automate the process of identifying common misconfigurations.
- Wireshark “Sniffing tool”: Wireshark has been running since 1998. Its main function is for debugging, identifying, and investigating any form of computer network. You don’t need to be a Wireshark expert, but you should be able to use basic filters to identify the traffic you are investigating.
- NESSUS “Vulnerability Scanner”: Generally, the commercial/professional versions of Nessus is a favourite of penetration testing companies. However, Nessus also supports a free version, Nessus Essentials.
- Burpsuite “Professional/Community”: If you are going to be testing web applications on a commercial level, you are almost certainly going to be using Burpsuite. Burpsuite has several configurable tools that are vital when learning to be Penetration Tester, such as the Intruder, Repeater, Comparer, and Decoder tools. You can also use OWASP Zap if you are on a limited budget, Zap is an open-source tool that has much of the functionality of Burpsuite.
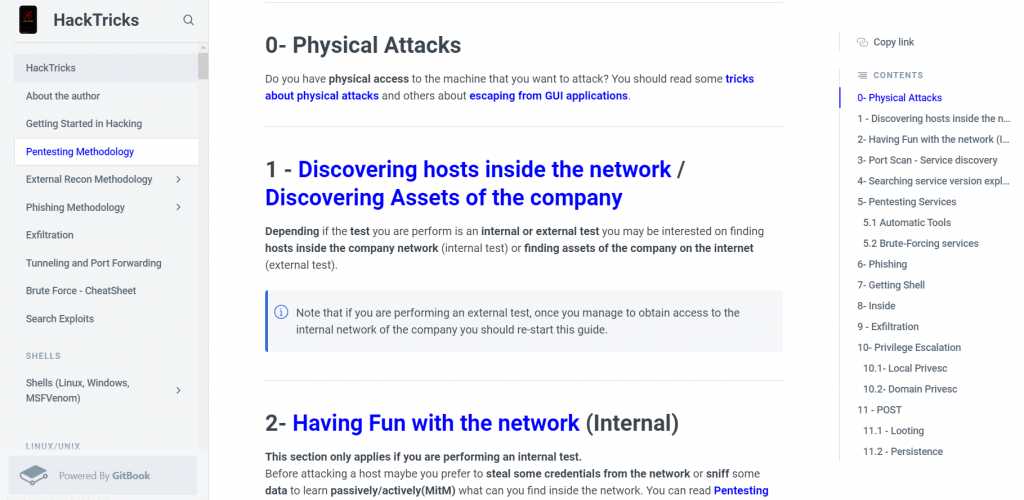
Hack Tricks
There are so many other tools and listing these in this post would make it very convoluted and it would seem very daunting. If there was one resource on the internet I could direct your attention to, it’s almost certainly HackTricks. This repo has been compiled over a long period of time, it contains so much information that can be absolutely vital to learning to become a proficient penetration tester. If you want to launch your penetration testing career. Take a look at the HackTricks GitBook.
HackTricks – The Holy Bible.
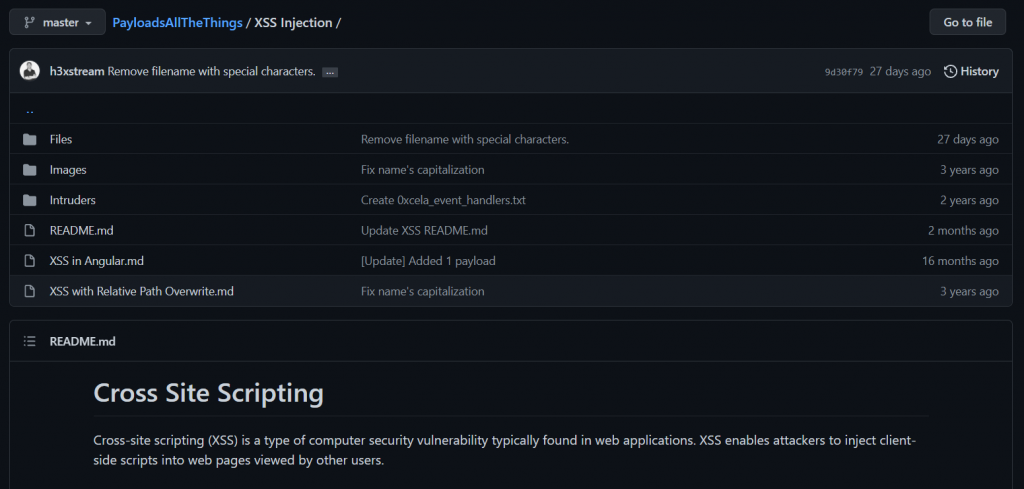
Payload All The Things
I cannot stress enough how reading through this git repo is going to help you. There are many nuggets of information to absorb. It has wordlists, files, and several great pieces of information on many attack vectors when it comes to various forms of testing. Download the repo here. Then open it in your favourite text editor, we like to use sublime. But each to their own.
Seclists
If we are mentioning fantastic repos, we cannot leave out this resource from Daniel Miessler. Seclists is used daily by most penetration testers. I couldn’t put it better than Daniel has here.
‘SecLists is the security tester’s companion. It’s a collection of multiple types of lists used during security assessments, collected in one place. List types include usernames, passwords, URLs, sensitive data patterns, fuzzing payloads, web shells, and many more. The goal is to enable a security tester to pull this repository onto a new testing box and have access to every type of list that may be needed.’
– Daniel Miessler
What certifications are required to become a Penetration Tester?
While certifications are not an absolute requirement to starting a career in penetration testing. Certifications will help prove to a potential employer that you can walk the walk, and not just talk the talk. What certifications do employers look for? This is very country-specific. Most Western countries will look for well-established certifications that don’t just test your theoretical skills. They also test your practical skills in finding, exploiting, and documenting vulnerable assets. Having practical-focused certifications can prove to an employer you have the skills to find, exploit, and document security issues.
Common Certifications employers ask for.
- Offensive Security Certified Professional (OSCP)
- CREST Practitioner Security Analyst (CPSA)
- CREST Registered Tester (CRT)
- eLearnSecurity Junior Penetration Tester (eJPT)
- eLearnSecurity Certified Professional Penetration Tester (eCPPT)
- CREST Certified Web Application Tester (CCT-WEB)
- CREST Certified Infrastructure Tester (CCT-INF)
Where can I practice Penetration Testing?
There are several places on the internet where you can practice your penetration testing skills. Gone are the days of setting up a Virtual Environment (Vmware, Virtualbox). So many businesses and start-ups have capitalised on the increasing popularity of Penetration Testing Careers. Some of these are listed below, we implore you to check out these resources.
Why does Penetration Testing have such a high barrier of entry?
As you explore various online platforms to practice your penetration testing skills, it’s equally important to understand the real-world implications, including the costs associated with professional penetration testing services. It is important to consider that your skills will be utilised by a company to sell penetration testing services, therefore highly specialised individuals are required to conduct these assessments. Very few companies want inexperienced individuals conducting assessments and representing them on a professional level. This is for obvious reasons, a badly conducted assessment can reflect badly on the company involved. Penetration testing is a considerable investment for a company and they (rightly) want the most comprehensive assessment possible.
For those interested in not just learning but also understanding the commercial aspect of penetration testing, our detailed guide on the costs involved in different types of penetration testing assessments in 2024 can be found here.
Conclusion
A penetration testing career can be a lucrative, rewarding career. It requires persistence, tenacity and gallons of caffeine. Although it can be daunting at first, once you become proficient in several areas, the confidence builds and the imposter syndrome starts to fade. Of course, we are slightly biased considering this post has been written by a penetration tester, and for the budding penetration tester. The security community is a tight-knit, supportive community. If you have questions about a specific topic, or you need some guidance. There will be many people who will help you along your path to becoming a penetration tester.
Frequently Asked Questions
Graduate or junior penetration testers can expect to earn between £20,000 and £30,000 as a starting salary. With experience, you can earn between £40,000 and £65,000, with senior and team leader roles often paying up to £70,000 +
In the United States, the average penetration tester income is $119,000 per year, and the starting salary for entry-level positions is $97,500 per year, with most experienced individuals earning up to $156,000 per year.
The short answer is yes, you can become a penetration tester without a formal degree. While a degree in computer science or a related field can offer a strong foundational understanding of the principles that underlie computer systems and networks, it’s not a strict requirement for entering the field of penetration testing. Many successful penetration testers have built their careers on self-taught skills, hands-on experience, and industry-recognised certifications.
Professional certifications like CREST (Council of Registered Ethical Security Testers) and OSCP (Offensive Security Certified Professional) are highly valued in the industry and can serve as a viable alternative to a formal degree. These certifications not only validate your technical skills but also demonstrate a commitment to professional development and adherence to industry standards. They can be particularly beneficial for those who are transitioning from other IT roles or are entering the cybersecurity field from a different background.
It’s worth noting that the cybersecurity landscape is ever-evolving, and penetration testing is a field that demands continuous learning. Whether you have a degree or not, staying updated on the latest vulnerabilities, attack methodologies, and security tools is crucial. Online courses, webinars, workshops, and even hacking forums can serve as valuable resources for skill development.
Additionally, practical experience is invaluable. Many aspiring penetration testers gain initial experience through internships, freelance projects, or even by setting up controlled environments to practise their skills. Real-world experience allows you to apply theoretical knowledge in practical scenarios, making you more attractive to potential employers or clients.
While a degree can provide a helpful foundation, it’s not an absolute necessity for a career in penetration testing. A combination of industry certifications, continuous learning, and practical experience can serve as a robust alternative pathway into this dynamic and rewarding field.
A career in penetration testing is not only rewarding but also comes with excellent salary prospects. Those who work in this field often find themselves at the forefront of security research, making significant contributions to the ever-evolving landscape of cybersecurity.
Embarking on a journey to become a penetration tester, commonly referred to as a ‘pentester,’ opens up a plethora of career options within the broader security industry. The skills and knowledge you acquire can be applied to various roles, making you a versatile professional in a sector that is increasingly critical in today’s digital age.
Yes, it is a common misconception that penetration testers do not need coding skills. However, they are often required to analyse the source code of a given exploit. Given this responsibility, the tester must understand what the exploit does, and the effects. While a Penetration Tester could almost certainly start their career without adequate coding skills, acquiring such skills is highly beneficial. Python and Bash are the recommended programming languages to learn, primarily because a clear majority of scripts are written in Python.
A licensed penetration tester typically refers to a penetration tester who holds relevant industry certifications that qualify the individual to conduct penetration testing. The relevant certification can vary depending on geographical location. In the UK for example, CREST is the leading certification body that certifies Penetration Testers in the UK.
Penetration Testing skills are amongst the most sought-after skills in Cyber Security. This demand is driven by the high barrier to entry to the profession and the rapidly growing need for penetration testing services around the world. It is projected that the market for penetration testing services in the United States will surpass $5 billion annually by 2031. The job market for penetration testing professionals is showing no signs of slowing down. 2024 is a great time to start your career in penetration testing.